- Implement Slack workflows to monitor unauthorized app usage, curbing Shadow IT.
- Utilize bots to automate routine tasks, reducing manual oversight and operational risks.
- Leverage Slack’s integration with cloud services to track and optimize resource usage.
- Enhance data security by centralizing communications and controls within Slack.
- Promote collaboration without compromising on IT governance or budgetary constraints.
“Automate Slack meticulously. Clamp down on shadow IT immediately. Optimize cloud expenses aggressively. Prioritize these actions. No exceptions tolerated.”
The Trojan Horse Directive Slack Automation, Shadow IT, and Cloud Cost Optimization
The Mass Illusion
In today’s hyper-digital landscape, Slack’s casual collaboration vibe has captivated professionals and startups alike. What surfaces as a charming docility is really a potent channel of potential disruption. Who doesn’t harbor dreams of achieving the silk-smooth, on-the-fly communication that seems to defy traditional team alignment barriers? Yet, amidst this digital utopia lies a much more compelling narrative, veering towards uncharted territories of efficiency and automation.
Why this fascination? Because Slack has become more than just a chat application; it’s our digital headquarters. Every workflow, every task, and every brainstorm finds its genesis on this singular platform. But beneath its polished user interface, we risk welcomed intrusions that may metamorphose into serious organizational pitfalls. Let’s talk Shadow IT.
The Enterprise Trap
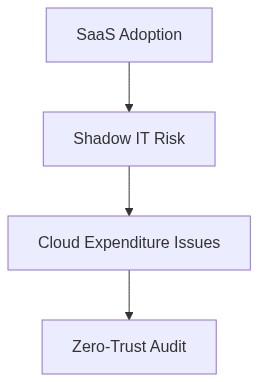
The decisively unregulated proliferation of Shadow IT, marked by untracked and unsanctioned tools, places enterprises at greater risk than ever before. As more employees introduce unapproved applications through what seems like benign Slack automations, corporations risk profound security breaches and increased vendor lock-in.
“By 2027, 50% of cloud security failures will be the result of shadow IT and insufficiently controlled information systems.” – Gartner
This lightning-fast tooling adoption opens floodgates not merely to vulnerabilities but to spiraling infrastructure costs. The hard data paints a daunting reality and accentuates the necessity for a robust Zero-Trust framework intertwined with a diligent approach to FinOps across your cloud architecture.
Enter the era where controlling shadow IT is no longer optional. The elucidated clarity of security protocols only marks half the journey; the other half warrants economic insights—unveiling and correcting cloud cost anomalies.
“CIOs must evolve to become experts in FinOps, ensuring rapid cost optimization across increasingly complex cloud environments.” – McKinsey
Questions Your Action Plan
Step 1 (For Smart Users) Start by examining your existing Slack integrations. Are these tools aligning with your organization’s endorsed IT framework, or do they teeter on the fringes of sanctioned use? Implement alerts for unrecognized application usage to delineate potentially problematic Shadow IT activities.
Step 2 (For IT Leaders) Prioritize establishing a strict Zero-Trust model. Resource access must hinge upon rigorous authentication and least privilege principles. Catalyze this model by consolidating disparate application management under a unified policy.
Step 3 Initiate comprehensive FinOps practices. Employ thorough data-driven insights to pinpoint and manage cloud cost anomalies. Collaborate with financial stakeholders to enable transparency in billing, forecasts, and risk assessments. Building a proactive culture around cloud financial management is indispensable.
As we delve deeper into this age of connectivity and digitization, the agility with which organizations respond to these looming challenges will define the next era of enterprise success. Embrace the disruptive prowess of Slack with an eye towards vigilant oversight and seamless cost management. For it’s amidst the whispers of automation that shadows grow, and only by bringing them to light can enterprises truly perfect their architectural fortresses.
| Parameter | Slack Automation Control | Optimize Cloud Costs | Security Risk Management |
|---|---|---|---|
| Productivity Impact | High | Medium | Low |
| Cost Efficiency | Medium | High | Medium |
| Security Risk | Medium | Low | High |
| Implementation Complexity | Low | Medium | High |
| Scalability | High | High | Medium |
| User Experience | High | Medium | Low |
Today’s enterprises must embrace the advantages of Slack automation while maintaining control and security. To achieve this intelligently and sustainably, take the following steps
1. Establish a Governance Framework
Define clear policies and guidelines for the use of Slack and related automation tools to prevent shadow IT. Ensure that all automation initiatives align with the organization’s strategic objectives and compliance requirements.
2. Implement Slack Automation
Begin integrating Slack automation by identifying and prioritizing key areas where automation can deliver the most value. Use Slack’s vast ecosystem of integrations to enhance collaboration while streamlining workflows and reducing manual effort.
3. Monitor and Manage Slack Use
Continuously monitor Slack usage and the applications connected to it. Use analytics to gain insights into how users interact with the ecosystem. This will help identify potential areas of optimization and prevent unauthorized application use.
4. Enhance Security and Compliance
Ensure that all Slack automation and integrations meet organizational security standards. Implement access controls and data encryption to protect sensitive information traveling through the cloud. Regularly review security protocols to adapt to evolving threats.
5. Foster a Culture of Innovation
Encourage employees to explore creative solutions leveraging Slack automation. Provide training and resources to empower teams to use automation effectively while maintaining a focus on security and governance.
By integrating these practices, enterprises can harness the full potential of Slack automation, driving innovation and efficiency while minimizing risks associated with shadow IT.”