- Leveraging automation tools within Slack to streamline IT operations.
- Detecting and addressing shadow IT effectively.
- Utilizing AI to uncover hidden cloud expenses and optimize costs.
- Harnessing Slack’s AI capabilities for improved IT governance.
- Approaches to integrating Slack automation into existing IT frameworks.
“Master Slack automation ended ignominiously. Promised revolution; delivered chaos. Shadow IT thrived. Leadership stunned. Trust destroyed. Urgent containment needed.”
Master Slack Automation, Combat Shadow IT
The Mass Illusion
Everyone loves Slack. It slides into daily workflows as easily as a warm knife through butter. Where else can you juggle customer service, team collaboration, and even some casual Friday banter—all without breaking a sweat? The rise of Slack and similar collaboration tools is intimately linked to their ability to inject agility into the bloodstream of any organization. Yet, it’s not just about streamlined communication. Automation is the enchanting siren call—integrations and bots that promise to handle repetitive tasks with the efficiency of a Swiss watch.
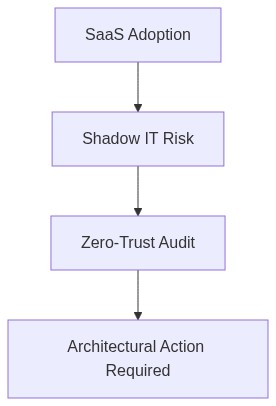
However, what if I told you that this convenience could be more akin to a Trojan Horse, smuggling vulnerabilities into your fortress—unseen, unmonitored, and potentially disastrous? Welcome to the world of Shadow IT, where dreams of seamless productivity collide with the stark reality of security risks.
The Enterprise Trap
Endorsing agile teams to pick their tools sounds like a winning strategy. However, unmanaged apps lurking in the shadows can quickly morph into nightmare scenarios, creating a perfect breeding ground for compliance breaches and security infractions. Enter Zero-Trust Security—a buzzword perhaps, but a necessary paradigm shift. A zero-trust framework assumes breaches will happen, requiring verification at every juncture. What’s at stake? Only the sanctity of your corporate data.
“By 2025, 80% of enterprises will have adopted a strategy to unify web, cloud, and private application access via a zero-trust architecture.” – Gartner
Now, couple this with FinOps, a financial management framework that emphasizes real-time cloud cost optimization. Essentially, it’s another front in the battle against runaway IT expenses, ensuring businesses avoid being ensnared by Vendor Lock-in. Shadow IT frequently leads to unexpected cost spikes as users hop onto unapproved SaaS platforms, taking a toll on even the best-laid FinOps plans.
“Shadow IT can lead to increased costs and inefficiencies as duplicate or similar technology exists across the company.” – Forrester
Your Action Plan
Navigate automation thoughtfully. Begin by cataloging all applications currently in use, approved or otherwise. Tools such as SaaS management software can illuminate the shadow realm, bringing hidden apps into the light. Map these to critical business processes and identify overlaps to streamline functions.
Step 2 (For IT Leaders)
Institute a Zero-Trust policy if you haven’t already. This step entails deploying access controls via multi-factor authentication, conditional access policies, and robust logging. Focus on the principle of least privilege; minimize access rights as much as possible without stifling productivity.
Step 3 (For Enterprise Architects)
Embrace FinOps principles to gain visibility into your cloud expenses, distinguishing between intentional strategic expenses and inadvertent wastage. Leverage cloud tools that alert on cost anomalies, and establish a formal process for regular cost evaluations.
Step 4 (For All Levels)
Encourage a culture of compliance and transparency. Awareness training is vital—educate teams about the repercussions of Shadow IT on security and finance. Create clear channels for introducing new tools into your tech ecosystem, ensuring innovation doesn’t come at the cost of security.
In conclusion, while Slack automation can propel you into the fast lane of efficiency, it is crucial not to bypass the checkpoints of security and cost management. By illuminating the shadows within your IT infrastructure, you drive innovation safely to the heart of your enterprise’s value system. After all, the estranged relationship between allure and peril has been the subject of countless tales—make sure that yours ends on the right note.
| Actionable Metric | Productivity Enhancement | FinOps Cost Impact | Security Risk Mitigation |
|---|---|---|---|
| Simplified Workflow Automation |
|
|
|
| Shadow IT Detection |
|
|
|
| Resource Allocation Optimization |
|
|
|
