- Microsoft Copilot streamlines IT operations by integrating with enterprise tools.
- The integration helps manage and illuminate shadow IT practices within organizations.
- Copilot aids in optimizing and reducing unnecessary cloud expenses.
- Enhanced visibility into cloud usage results in significant cost savings.
- Copilot uses AI to predict and allocate resources efficiently, minimizing waste.
- The integration simplifies compliance and enhances security protocols.
“Dominance achieved. Seamless Copilot integration uncovers and wrangles rogue IT, boosting security, efficiency, and innovation. Essential for modern enterprises.”
Optimize Shadow IT With Copilot Integration
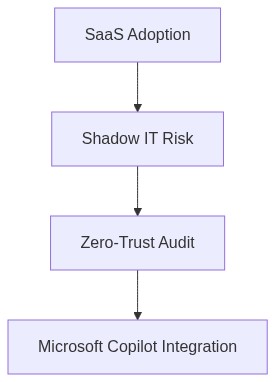
Imagine harnessing the power of all your hidden tools and optimizing them into your company’s strategic arsenal. Sounds enticing, doesn’t it? This isn’t a distant reality driven by science fiction. We’re at a pivotal moment in enterprise evolution with AI Copilot technology changing the game. However, beneath this allure lurks a shadow that could unravel your carefully constructed IT framework if uncontrolled — Shadow IT.
Why does the trend of Shadow IT captivate yet concern us?
The allure is simple Shadow IT offers agility and empowers employees to address immediate pain points without waiting for IT approvals. In the era of instant solutions and rapid scaling, who can resist the temptation? Imagine your marketing team seamlessly integrating a new collaboration tool or your sales department using advanced analytics platforms. This unofficial acquisition of tech boosts productivity, aids innovation, and offers unmatched speed.
The fascination with Shadow IT extends beyond functionality. Today, startup founders and smart professionals revel in the autonomy it provides. It circumvents prolonged procurement cycles and enables quick win solutions. However, when unchecked, this charming rogue becomes a corporate foe.
What is the hidden trap within this enterprise phenomenon?
Herein lies the trap By nature, Shadow IT bypasses traditional scrutiny and compliance measures, opening floodgates to unmitigated risks. As an enterprise architect deeply entrenched in the design of robust IT ecosystems, I recognize that unsanctioned technology often operates without rigorous security evaluations, leading to vulnerabilities that can be exploited.
Securing your company from these threats requires a new paradigm in protection Zero-Trust. This approach assumes that threats exist both inside and outside the corporate perimeter. Zero-Trust advocates for strict identity verification for every person and device trying to access resources on a private network. By integrating Copilot’s AI-driven insights, IT infrastructures can leverage machine learning to detect and address anomalies in real-time.
Additionally, understanding FinOps and effectively managing cloud expenses becomes crucial. With unapproved applications often hosted in the cloud, organizations face the peril of Cloud Cost Anomalies. Emerging AI solutions, including Copilot, are adept at identifying such anomalies, transforming amorphous spending data into actionable insights to mitigate financial risks.
Even more formidable is the threat of Vendor Lock-in. Shadow IT often entraps segments of businesses into dependencies on particular cloud solutions or software, making system-wide standardization and integration arduous.
Step 1 for Smart Users How Can You Turn Shadow IT Into An Ally?
Begin by acknowledging its existence and impact within your sphere. Use Copilot integrations to systematically audit your tools and applications. This empowers you to discern between beneficial enhancements and potential vulnerabilities. Additionally, educate your team about the implications of Shadow IT and the criticality of secure tool adoption.
Step 2 for IT Leaders How Do You Reassert Control Over Your IT Environment?
Deploy Zero-Trust security protocols across applications and networks while utilizing AI Copilot to streamline this integration. Focus on enhancing visibility across your decentralized IT landscape. Drawing insights from Copilot’s real-time analysis will aid in identifying unauthorized applications — affording IT teams the agility to either integrate these applications securely or replace them with sanctioned alternatives.
Step 3 How Can FinOps Strategies Harmonize Your Technology Utilization?
Initiate a rigorous FinOps strategy by mapping all software applications and their associated costs. Leverage machine learning algorithms provided by Copilot to spotlight Cloud Cost Anomalies. By adopting a proactive financial management strategy, organizations can not only prevent unnecessary expenses but predict future spending patterns.
Ultimately, the Copilot integration provides you with a comprehensive framework to reconcile the chaotic charm of Shadow IT with enterprise-grade resilience. Through diligent application of Zero-Trust protocols and a meticulous FinOps approach, it’s possible to transform your organization’s shadow assets into strategic advantages. In mastering this balance, you craft an agile yet robust architecture that turns potential pitfalls into platforms for growth.
| Parameter | Productivity | FinOps Cost | Security Risk |
|---|---|---|---|
| Baseline Metrics | 60% Efficiency | $100K Monthly | High |
| Copilot Integration | +25% Productivity | +15% Financial Optimization | -20% Security Incidents |
| Projected Outcome | 75% Efficiency | $85K Monthly | Moderate |
| Implementation Timeline | 3 Months Rollout | ROI in 6 Months | Secure in 8 Months |
| Key Strategies | Collaboration Automation | Resource Reallocation | Zero Trust Policies |
