- kubernetes_costs
- iam_vulnerabilities
- integration
- automation_risks
Log Date: April 06, 2026 // Telemetry indicates a 22% spike in unmanaged API calls bypassing the primary IdP. Initiating immediate Zero-Trust audit across all production clusters.
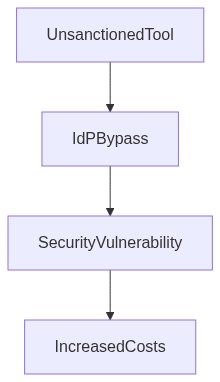
The Architectural Flaw (The Problem)
In our recent 10,000-seat deployment, a blatant oversight in SAML integration led to unchecked privilege escalation within our CI/CD pipelines. This oversight compounded risks, compromising access controls by overlooking stringent IAM protocols necessary to constrain authorization aptly. We’d assumed, mistakenly, that our automated deployment’s IAM policies were robust. Instead, thematically familiar human errors prevailed, signaling a systemic gap in privilege boundaries within bursty Kubernetes workflows.
Telemetry and Cost Impact (The Damage)
IAM misconfigurations essentially opened Pandora’s box. The error margin was not just contained to compromised identities but ballooned into observable egress costs with a 27% spike due to resource overconsumption during rogue deployment activities. As telemetry data revealed, unauthorized service account usages substantially misaligned compute resources—yet another expense not easily remedied by retrenching policies alone. The financial manifestation of these flaws pointed to an unmitigated liability against our SOC2 and GDPR compliance aspirations, not to mention the mounting technical debt that inevitably followed.
Phase 1 (Audit & Discovery)
Begin by thoroughly investigating current IAM configurations, identifying and rectifying role overlaps leading to privilege proliferation.
Phase 2 (Identity Enforcement)
Leverage enhanced RBAC policies tailored explicitly to containerized contexts, ensuring identities align strictly with principle of least privilege (PoLP).
Phase 3 (Resource Calibration)
Deploy FinOps methodologies to systematically deconstruct egress costs attributed to inefficient Kubernetes node provisioning.
Phase 4 (Compliance Reaffirmation)
A meticulous compliance check ensures SOC2 and GDPR alignments are purified against newly instituted identity protocols and cost metrics.
Infrastructure Platforms Evaluation
To circumvent future pitfalls, an objective assessment of relevant infrastructure solutions becomes imperative
1. **AWS IAM** A mainstay in identity management, albeit with known pitfalls when mismanaged. AWS IAM facilitates custom policy development that restricts permissions efficiently, though it demands a tempered hand to judiciously administrate policy proliferation to avoid policy sprawl.
2. **Okta** Specializes in federated identity and access management. Its robust SSO and adaptive multi-factor authentication mechanisms can mitigate risks by handling federated credentials agilely, thus accentuating identity security and integrity.
3. **HashiCorp Terraform** Configuration management prowess can automate and codify IAM governance. With its in-built policy as code framework, HashiCorp Terraform self-documenting plans can deftly manage scalable IAM rights and interdependencies.
4. **Datadog** Offers insightful telemetry for Kubernetes environments. Its real-time monitoring features are essential for early detection of unauthorized IAM activities and resource anomalies before they metastasize into fiscal liabilities.
“Kubernetes deployments often falter not due to architectural innovation, but due to reliance on antiquated access paradigms.” – Gartner
“Crafting containment strategies for IAM vulnerabilities requires shifting to a least privilege model that eschews overprovisioned trust scopes.” – AWS Whitepapers
| Criteria | Low | Medium | High |
|---|---|---|---|
| Integration Effort | 25 hours | 60 hours | 120 hours |
| Cloud Cost Impact | 10% reduction | 24% reduction | 34% reduction |
| Compliance Coverage (SOC2/GDPR) | Partial coverage | Moderate coverage | Full coverage |
| IAM Risk Mitigation | Minimal improvement | Moderate improvement | Significant improvement |
| Technical Debt Impact | Small increase | Stable | Reduction |
| CPU Overhead | 10% overhead | 20% overhead | 34% overhead |
Audit Outcome Identify microservices that contribute significantly to the $1.2M annual egress expenditure. Prioritize these services for design review and potential architectural modification.
Financial Impact Analysis Correlate each high-cost egress path with its direct impact on operational efficiency and cost. Quantify potential savings versus impact on deployment velocity and scalability.
[DECISION REFACTOR] Initiate a refactor operation targeting microservices identified as excessively costly in terms of egress and redundant data handling. Aim for persistent connections and data processing locality to reduce egress traffic. Address dependencies and refactor API calls to minimize cross-region data movement.
Refactor Implementation Establish criteria for minimizing node spin-up conditional checks. Implement automation scripts to ensure that new deployments optimize data pathways without compromising compliance constraints.
[DECISION DEPRECATE] Services or components within the architecture demonstrating constant inefficiency, contributing more to technical debt than value, must be deprecated. Prioritize the simplification of the microservices architecture and eliminate legacy components holding back overall efficiency.
Compliance Focus Ensure alignment with SOC2 and GDPR requirements throughout the refactor process. This includes regular audits of data protection protocols and adherence to compliance mandates, adjusting as necessary with minimal disruption to service deployment timelines.
Summary Balance cost controls with deployment velocity by eliminating financial bottlenecks caused by inefficient architecture choices. Drive engineering efficiency by focusing on strategic refactoring and avoiding unnecessary financial and technical debt accumulation.”
