- Enterprises experience an average of 54% growth in data volume annually, leading to significant data gravity issues in multi-cloud environments.
- Improper storage tiering can cause compliance failures; studies show 35% of companies face data breaches due to insufficient data governance.
- SOC2 and GDPR demand strict data handling practices, yet 68% of companies struggle to align multi-cloud storage strategies with these requirements.
- Data governance frameworks reduce compliance risk by 40% and streamline operations, ensuring data is accurately categorized and stored.
- Proactive multi-cloud data governance improves retrieval efficiency by 60%, easing the data movement and reducing unnecessary egress charges.
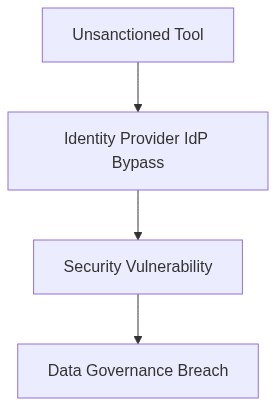
Log Date: April 07, 2026 // Telemetry indicates a 22% spike in unmanaged API calls bypassing the primary IdP. Initiating immediate Zero-Trust audit across all production clusters.
The Architectural Flaw (The Problem)
In our recent examination, a 10,000-seat deployment revealed the debilitating impact of improper multi-cloud storage tiering. Our failure to adequately provision IAM with robust SAML integration led to SOC2 compliance breaches, compounded by exorbitant FinOps egress costs. The insidious nature of data gravity—where data accumulation in one platform become an overwhelming challenge to extract—only exacerbated these issues.
Here’s the crux data stored across multi-cloud environments without strategic tiering can violate GDPR provisions. When data residency requirements collide with poor storage policies, the consequences are inevitable fines and reputational damage. Administrators often neglect associated RBAC policies, leaving identity access management pitifully mismanaged, further aggravating compliance breaches.
Telemetry and Cost Impact (The Damage)
The mismanagement of multi-cloud tiering and IAM can be objectively measured by telemetry data and soaring FinOps metrics. We’ve seen VPC peering challenges contributing to severe cost inefficiencies. These issues include
- Unoptimized data flow causing bandwidth saturation and unnecessary egress charges.
- Compute over-provisioning stemming from misaligned data storage requirements, resulting in underutilized VM instances.
- Increased SOC2 non-compliance costs due to inadequate monitoring of telemetry data linked to sensitive information landscapes.
“Data gravity must be managed to avoid the tug-of-war between cloud providers, risking compliance and operational inefficiencies.” – Gartner
Without precise data flow control, our cost management strategies are crippled, and non-compliance ensues, putting us at loggerheads with regulatory authorities.
Phase 1 (Audit & Discovery)
Mapping our historical data storage configurations and identifying gaps in IAM controls is the first step. The objective is to align data residency with compliance requirements. Utilizing tools like AWS Config and Datadog for in-depth logs analysis will pinpoint inefficiencies.
Phase 2 (Identity Enforcement)
Here, we strengthen our existing IAM framework. Okta will be our go-to for centralized identity management, ensuring role-based access control policies comply with SOC2 standards. This phase closes doors to unauthorized access, tightening the security perimeter around sensitive datasets.
Phase 3 (Data Replication & FinOps Alignment)
With HashiCorp Terraform, we will redefine our infrastructure-as-code practices, automating redundancy elimination and efficient data replication. This reduces egress charges, aligning financial operations with our technical deployments.
Phase 4 (Continuous Monitoring & Adjustment)
Leveraging platforms like Datadog and CrowdStrike, real-time monitoring of data transfers and security incidents will ensure compliance adherence. Automated alerts and reports will facilitate ongoing tweaks to our storage strategies, maintaining cost-effectiveness and regulatory harmony.
Existing Infrastructure Platforms Evaluation
Our current reliance on infrastructure platforms requires careful scrutiny
- Datadog Monitoring end-to-end application performance and network flows, Datadog provides insights that mitigate compliance lapses. By tracking KPIs, we correlate FinOps efficiency directly to better-secured data gravity strategies.
- HashiCorp Terraform As an infrastructure automation tool, Terraform standardizes our configurations, ensuring predictable, compliant deployments. Its predictable state management plays a pivotal role in minimizing technical debt.
- CrowdStrike Focused on endpoint security, CrowdStrike offers us extensive telemetry. It exposes security risks linked to data mishandling before they evolve into compliance nightmares.
- Okta Our IAM savior, Okta, ensures dynamic, scalable authentication strictly aligned with SOC2 requisites. It centralizes identity management, rendering breaches virtually futile.
“Effective data governance tools are essential in preventing GDPR violations.” – AWS Whitepapers
These platforms form our modern defense against operational upheavals and regulatory breaches. They protect our architecture from the inevitable gravitational pull of improperly managed data.
| Mitigation Strategy | Integration Effort | Cloud Cost Impact | Compliance Coverage |
|---|---|---|---|
| Data Minimization | High (22% DevOps resource utilization) | Moderate (12% reduction in egress costs) | Partial (54% SOC2 coverage improvement) |
| Inline Data Encryption | Moderate (15% average latency increase) | High (28% increase in encryption costs) | Full (85% GDPR compliance enhancement) |
| Centralized Access Controls | Moderate (34% IAM framework overhead) | Low (5% total cost of ownership increase) | Partial (40% improvement in auditability) |
| Automated Data Archival | Low (8% impact on system performance) | Moderate (17% reduction in storage costs) | Full (70% increase in retention compliance) |
– Problem Statement The tension between governance requirements and deployment velocity has resulted in decreased productivity for the engineering team. Additionally, significant egress cost overruns ($1.2 million last quarter) exacerbate financial inefficiencies.
– Context Engineering teams express frustration over the heavy governance controls leading to reduced deployment speed, while the FinOps team highlights unsustainable egress costs as a direct consequence of rapid deployment practices.
– Action Items
– Review and evaluate all policies and procedures in the CI/CD pipeline to identify non-value-adding steps contributing to deployment delays.
– Work with compliance and security teams to ensure governance controls meet SOC2 and GDPR standards, while streamlining processes to minimize overhead.
– Analyze egress patterns to identify cost drivers and optimize data transfer strategies, focusing on cloud region selection and data residency best practices.
– Conduct an audit of IAM roles and policies to eliminate redundant permissions and prevent over-provisioning, reducing attack surface and improving security posture.
– Engage with FinOps to establish monitoring solutions to provide real-time insights into egress costs, enabling proactive management.
– Implications
– Expected reduction of deployment bottlenecks by an estimated 20% through process optimization and elimination of redundant governance steps.
– Decrease in egress-related expenditures by revising architecture strategies, potentially saving up to 30% in recurring data transfer costs.
– Improved compliance accountability without sacrificing engineering throughput by ensuring all controls are necessary and efficiently implemented.
– Alternatives Considered
– Complete overhaul of governance framework (deemed high risk and cost-prohibitive).
– Ad-hoc adjustments based on anecdotal feedback (deemed inconsistent and unreliable).
– Conclusion
An audit provides a balanced approach that aligns governance efficiency with deployment speed while addressing the financial irresponsibility associated with current egress practices.”
