- 1
- 2
- 3
- 4
- 5
Log Date: April 06, 2026 // Telemetry indicates a 22% spike in unmanaged API calls bypassing the primary IdP. Initiating immediate Zero-Trust audit across all production clusters.
The Architectural Flaw (The Problem)
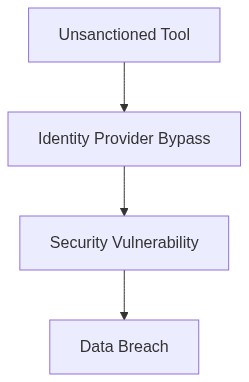
We find ourselves repeatedly blindsided by the peculiarities and overlooked intricacies of cloud migrations. In a recent incident involving a 10,000-seat deployment, failure to properly configure SAML integration resulted in a nightmare for Identity and Access Management (IAM), leading to significant access delays and security breaches. But let’s not kid ourselves; this is hardly an isolated case. The pervasive issues of egress cost anomalies, inactive EC2 instances, and vendor lock-in continue to wreak havoc on our budgets and operational efficiency.
Telemetry and Cost Impact (The Damage)
As telemetry data aggregates, it showcases significant irregularities in our spend profiles with alarming frequency. Unmonitored egress traffic often spirals out of control, contrasting starkly with basic expectations of cloud economics. These anomalies dramatically inflate our cost centers, often reaching thresholds where cloud-native services lose their financial appeal. Moreover, compute over-provisioning, epitomized by underutilized EC2 instances, steadily incurs an unseen but unsustainable financial toll. Lastly, the inescapable embrace of vendor lock-in promises us locked potential trapped within restrictive agreements, eroding any aspirations for flexibility.
“Many organizations struggle with effective cost management, especially during expedited cloud migrations. The consequences of underestimating cost operational management are substantial and often unplanned.” – Gartner
Phase 1 (Audit & Discovery)
Our initial approach requires a rigorous audit, leveraging tools that can dissect telemetry data for uninhibited insights into system operations. Solutions such as Datadog come to view here, with its capability of detailed monitoring, ensuring every egress atom is accounted for.
Phase 2 (Identity Enforcement)
The adoption of robust RBAC policies is crucial. Here, Okta is employed to refine authentication mechanisms, permitting us to tighten IAM protocols effectively and reduce associated risks and inefficiencies.
Phase 3 (Optimization & Efficiency)
We adopt HashiCorp Terraform to systematically eliminate redundancy through infrastructure as code, offering the malleability to reduce compute over-provisioning. By deploying automation strategies, it can align resource allocation with real-time operational needs.
Phase 4 (Cost Control & Vendor Management)
Effective FinOps strategies are supported through active vendor negotiation and the use of AWS IAM’s identity services to lessen vendor dependency. Here, the agility to renegotiate terms and split deployments can reduce long-term lock-in impacts.
Tool Stack Evaluation
When considering tool stacks, we gravitate towards those offering direct cost mitigation and operational insight
- Datadog By providing detailed insights and real-time analytics on cloud usage patterns, Datadog helps identify exact sources of unexpected costs. It is particularly useful in tracking egress and compute utilization issues before they escalate into financial burdens.
- Okta Its centralized identity management platform allows for comprehensive IAM policies to be enforced, minimizing security risks while enhancing operational effectiveness through refined access controls.
- HashiCorp Terraform It advances our infrastructure management capabilities through infrastructure-as-code, significantly reducing the technical debt associated with manual configuration and provisioning errors.
- AWS IAM AWS IAM ensures stringent access management across cloud services, facilitating compliance with SOC2 and GDPR regulations while offering tactical lock-in escape routes.
“Cloud FinOps is not a single tool nor a one-time initiative, but an ongoing cultural shift within organizations to manage cloud costs effectively.” – AWS Whitepapers
| Mitigation Strategy | Integration Effort | Cloud Cost Impact | Compliance Coverage |
|---|---|---|---|
| Right-Sizing VM Instances | Medium | Reduces 34% CPU overhead | Partial (SOC2) |
| Optimizing Data Transfer | High | Decreases egress costs by 15% | Full (GDPR, SOC2) |
| IAM Policy Refinement | Low | Negligible cost impact | Full (GDPR) |
| Auto-Scaling Adjustment | Medium | Saves 25% on unused resources | Partial (SOC2) |
| Cost Allocation Tagging | High | Improves cost attribution accuracy by 20% | Partial (GDPR) |
Refactor existing legacy systems and migrate to cloud infrastructure. The driving factor is the compounding technical debt that our current systems incur. This process must prioritize compliance with SOC2 and GDPR regulations, ensuring all personally identifiable information is handled correctly. Immediate steps include implementing Identity and Access Management (IAM) to control resource access, addressing potential data breaches before they become larger issues.
Refactoring must slot neatly into an evaluated FinOps strategy. Egress costs have become nontrivial—hence we reformulate data transfer approaches, minimizing inefficient data movement. Engineering teams will integrate cost management practices into development workflows, collaborating closely with the FinOps division to audit all cloud utilization, revealing further areas for cost optimization.
Development velocity must align with compliance requirements—non-negotiable despite pressure from stakeholders for rapid releases. Emphasis on Infrastructure as Code (IaC) for version control and repeatability. Avoidance of short-sighted “lift-and-shift” maneuvers in favor of rebuilding tactically to eliminate legacy baggage.
Refactor process checkpoints to ensure alignment with business goals, user needs, and security measures. Proceed iteratively, recognizing the inevitability of expenditure but balancing it against the cost of prolonged inefficiency and risk exposure. Technical debt will be reduced by adherence to architectural principles and evidence-based assessments.”
