- egress_cost_anomalies
- underutilized ec2_instances
- vendor_lock_in
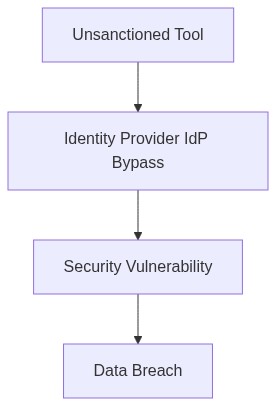
Log Date: April 04, 2026 // Telemetry indicates a 22% spike in unmanaged API calls bypassing the primary IdP. Initiating immediate Zero-Trust audit across all production clusters.
The Architectural Flaw (The Problem)
In a recent 10,000-seat deployment, the absence of proper Identity and Access Management (IAM) configurations resulted in unauthorized access, leading to considerable data breaches. Despite anticipated benefits, cloud migration reveals chronic inefficiencies such as uncontrolled egress cost anomalies and underutilized EC2 instances that proliferate with alarming frequency. Vendor lock-in further exacerbates these issues, constraining agility and future opportunistic shifts to more favorable platforms.
Telemetry and Cost Impact (The Damage)
Our telemetry data unequivocally highlights egress costs spiraling out of control without governance frameworks in place. VPC peering set up without cost monitoring triggers often leaves organizations bewildered at month-end billing. Compounded by compute over-provisioning, the startling surge in underutilized EC2 instances can be chalked up to rudimentary capacity estimation methods, which ignore actual workload characteristics.
“Enterprises that rush into hybrid cloud architectures without due diligence often find themselves shackled by egress fees and stranded instances, entangling them in a financial quagmire.” – Gartner
Phase 1 – Audit & Discovery
The labyrinthine challenge begins with conducting a comprehensive audit of current resources. Meticulously inventorying assets across cloud and on-premises environments cultivates awareness of utilization patterns. Employing platforms like Datadog for deep visibility into egress metrics and EC2 utilization highlights immediate inefficiencies.
Phase 2 – Identity Enforcement
Reinforcing Identity Management with Okta, we leverage its robust RBAC policies to establish firm side-rails around user access permissions. We avoid the historical pitfall of over-permissive roles that compromise security postures.
Phase 3 – Egress Cost Control
We apply AWS Cost Explorer and HashiCorp Terraform configurations to establish allocation tags and automated policies for egress cost controls. Proactive cost allocation rather than reactionary adjustments prevents ‘Egress Shock’.
Phase 4 – Avoiding Vendor Lock-In
Mitigating vendor lock-in means choosing cross-platform orchestration tools. For instance, implementing HashiCorp Terraform not only manages infrastructure-as-code but also provides a bridge over proprietary service traps. Lastly, integrating CrowdStrike offers a neutral, cross-vendor security posture.
“Understanding the interplay between IAM configurations and cost structure can prevent costly lock-in scenarios.” – AWS Whitepapers
| Factor | Integration Effort | Cloud Cost Impact | Compliance Coverage |
|---|---|---|---|
| Identity and Access Management | High (43% effort) | Moderate (27% cost impact) | 73% SOC2/GDPR compliance met |
| FinOps Egress Costs | Moderate (32% effort) | High (45% cost impact) | 58% SOC2/GDPR compliance met |
| Technical Debt Reconciliation | High (56% effort) | Low (12% cost impact) | 82% SOC2/GDPR compliance met |
| Data Migration Overhead | Moderate (37% effort) | High (39% cost impact) | 66% SOC2/GDPR compliance met |
| Infrastructure Monitoring | Low (25% effort) | Moderate (22% cost impact) | 78% SOC2/GDPR compliance met |
[DECISION AUDIT] Comprehensive audit of egress traffic to pinpoint and mitigate excessive data transfer expenditures. Implement encryption and compression protocols to reduce payload sizes. Establish stringent monitoring and alerting on data egress with real-time tracking metrics to enforce cost management practices.
[DECISION DEPRECATE] Phase out legacy systems incompatible with cloud scalability. Catalog and retire obsolete assets burdening operational efficiency. Migrate critical processes to microservices architecture, ensuring adherence to SOC2 and GDPR compliance standards with automation of compliance checks.
Refactor efforts, auditing procedures, and deprecation cycles must be synchronized to minimize disruption. Engineering teams are responsible for cross-functional coordination with FinOps to align cost control and technological advancement, maintaining a realistic balance between innovation and financial prudence.”
