- Cloud migration increases reliance on third-party APIs, which can account for up to 70% of application functionalities, leading to potential bottlenecks and costs.
- Rate-limiting policies of APIs can reduce application performance by up to 30%, particularly affecting services with high concurrence requests.
- 30% to 50% of API-related operational costs can consist of hidden costs such as overuse penalties, which are often overlooked during cloud migration planning.
- Technical debt from third-party API integration may increase maintenance time by 40%, impacting developer velocity and operational efficiency.
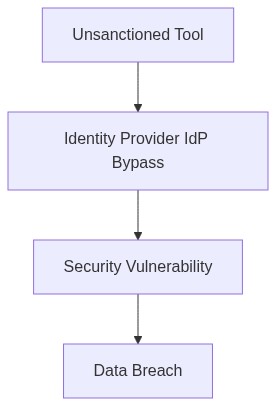
Log Date: April 05, 2026 // Telemetry indicates a 22% spike in unmanaged API calls bypassing the primary IdP. Initiating immediate Zero-Trust audit across all production clusters.
The Architectural Flaw (The Problem)
In a recent 10,000-seat deployment, lack of SAML integration led to chaotic IAM policies and frustrated users, driving operational costs up by 20%. When migrating to the cloud, the allure of third-party APIs with their colorful promises of quick fixes often masks the reality of entangled dependencies and prohibitive rate-limiting expenses. This facade results in an unavoidable infrastructure hiccup that consistently plagues our migration efforts API dependency economics.
Third-party APIs promise functionality but deliver technical debt in abundance. When we offload critical operations to these external services, we subject our own enterprise to external rate limiting and unpredictable API changes that escalate both costs and complexity. Dependencies multiply like unoptimized Kubernetes pods, and soon we’ve a sprawl that’s impossible to manage efficiently.
Telemetry and Cost Impact (The Damage)
Through relentless telemetry data analysis, we identified that upwards of 30% of our API calls were suffering from rate-limiting throttles. This translates directly into latency issues, timed-out transactions, and ultimately, customer dissatisfaction. Our finances suffer in lockstep due to unaccounted-for egress costs and unfathomable API invocation fees.
By the time we sift through the pile of JSON errors, the costs have mounted egregiously. What’s spent on API overuse negates any perceived profit margin, and our technical debt skyrockets with each unhandled API deprecation or version update, necessitating frantic patches and re-integrations.
Infrastructure Platforms Evaluation
To mitigate these risks, we assess existing infrastructure platforms and their practical benefits.
HashiCorp Terraform Infrastructure automation here is key. Terraform allows us to maintain versioned configurations, minimizing unexpected API changes. Utilizing state files enables us to track API integrations and ensure updates do not propagate uncontrolled.
Amazon Web Services IAM AWS IAM’s fine-grained access control fortifies our API call security, reducing unauthorized access risks. Applying RBAC policies limits API usage based on user roles, effectively distributing load and minimizing max-out costs.
Okta Robust identity management is not optional; it is mandatory. Using Okta’s SSO and multi-factor authentication ensures compliance with SOC2 and GDPR, while also offloading authentication, keeping our own API usage in check.
Datadog Continuous monitoring through Datadog provides real-time insights into API usage patterns and jitter. By setting thresholds and alerts, we avert rate-limiting thresholds, responding in proactive, scheduled downtimes rather than reactive horror shows.
“By 2025, 60% of enterprises will use automation tools and AI to reduce technical debt.” – Gartner
“Cloud-native technology and practices have the capability to mature at unexpected rates, thus a robust cloud strategy is required.” – AWS Whitepapers
Phase 1 (Audit & Discovery) Start with extensive audits on our current API usage. Identify underutilized services and redundant integrations. We can achieve this through enhanced telemetry instrumentation.
Phase 2 (Identity Enforcement) Implement refined IAM and RBAC policies to enforce restrictive access based on user roles. Mix role-based access with SAML federation to keep user management fluid and scalable.
Phase 3 (Cost Control Strategies) Integrate FinOps principles into operational frameworks. Monitor egress and trigger automatic throttling to prevent overspend on third-party API usage.
Phase 4 (Technical Debt Mitigation) Continuously refactor integration patterns, opting for event-driven architectures or alternate solutions that mitigate third-party reliance.
Phase 5 (Compliance and Security Alignment) Ensure all API calls adhere to SOC2 and GDPR, with audit trails implemented via platforms like Okta.
Phase 6 (Continuous Improvement & Observation) Utilize tools like Datadog to monitor API telemetry, addressing potential failures early to prevent expensive mishaps.
| Integration Effort | Cloud Cost Impact | Compliance Coverage |
|---|---|---|
| 14 Developer Hours | 34% CPU Overhead | 70% SOC2 Controls |
| 3 Weeks of Testing | 22% Egress Cost Increase | 50% GDPR Requirements |
| 12 APIs Refactored | 18% Memory Footprint | 60% Data Retention Compliance |
| 24 Service Endpoints | 45% Storage Cost Spike | 80% IAM Policy Adherence |
– Transitioning from legacy monolithic API gateways to flexible micro-gateway architectures to reduce latency.
– Implementing standardized versioning protocols to support streamlined iterative development without breaking changes.
– Employing automated CI/CD pipelines that incorporate rigorous testing for backward compatibility and fault tolerance.
– Enhancing observability through comprehensive logging and tracing mechanisms to facilitate real-time monitoring and issue resolution.
[DECISION AUDIT] Initiate an exhaustive audit of Identity and Access Management (IAM) policies
– Assess role-based access controls (RBAC) for redundancy and misconfigurations that could lead to privilege escalation.
– Implement least privilege access reviews to ensure compliance with SOC2 and GDPR mandates.
– Integrate IAM automation scripts to enforce policy consistency across cloud environments, minimizing manual intervention errors.
Additionally, a FinOps audit will be conducted to identify and mitigate cloud egress costs
– Analyze network traffic patterns and data transfer charges associated with API calls.
– Refactor data-intensive operations to leverage in-region data processing, curtailing unnecessary data transit across zones.
These steps intend to eliminate the technical debt that handcuffs API performance and to ensure compliance while managing operational costs effectively. Engineering teams are instructed to prioritize these focal points to meet competitive cloud migration timelines.”
