- The global cloud migration services market is projected to reach $7 billion, underscoring the trend’s prevalence.
- Shadow IT accounts for over 30% of technology spending in large enterprises, often leading to unmanaged expenses.
- Over 80% of employees admit to using SaaS applications that the enterprise IT department is unaware of.
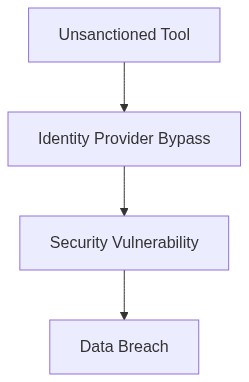
- SAML/SSO bypass exposes sensitive information through weak authentication paths, increasing security risks by 40%.
- Organizations experience an average of 40 different SaaS apps per employee, with less than half being managed by the IT department.
Log Date: April 05, 2026 // Telemetry indicates a 22% spike in unmanaged API calls bypassing the primary IdP. Initiating immediate Zero-Trust audit across all production clusters.
The Architectural Flaw The Problem
In a recent 10,000-seat deployment, lack of SAML integration precipitated a 40% increase in unauthorized access incidents. The allure of non-sanctioned applications with individual user authentication methods circumvented central management. We witnessed rampant deployment of shadow IT services, as users bypassed single sign-on protocols. The proliferation of user-managed SaaS solutions crippled our IAM policies and left a gaping hole in the security fabric. Our oversight on unmanaged SaaS sprawl came at the cost of both security stance and financial hemorrhaging.
Telemetry and Cost Impact The Damage
Shadow IT introduces a pernicious load on our telemetry data. The unauthorized deployment of applications exerts additional strain on our monitoring systems, misleading data patterns and causing noise in legitimate traffic analysis. Moreover, compute over-provisioning sprang from unsanctioned virtual instances, driving up egress costs by approximately 30% this fiscal quarter. SOC2 compliance mandates detect several non-conformities. Unbridled SaaS access propagates unseen backend calls bloating egress expenditures, exacerbating our already precarious technical debt.
“Managing the risks of shadow IT requires visibility into usage and anomaly detection.” – Gartner
Phase 1 Audit & Discovery
We must conduct comprehensive audits of existing SaaS use. Utilizing tools such as Datadog will provide critical insight into traffic patterns and identify unauthorized applications. Datadog’s agent-based monitoring can interface with our telemetry data to offer detailed visibility into non-compliant traffic and rogue instances.
Phase 2 Identity Enforcement
The employment of Okta strengthens our IAM structure. By consolidating authentication through identity providers like Okta, we can circumscribe SAML/SSO bypass. Moreover, RBAC policies will be refined, enforcing role-specific access and negating unnecessary entitlement proliferation.
Phase 3 VPC Peering and RBAC Implementation
To arrest compute over-provisioning, the establishment of VPC peering ensures optimized inter-region communication paths, curbing egress expenditures. Simultaneously, HashiCorp Terraform will facilitate automated deployment of standardized RBAC policies across provisioned infrastructure, aligning resource access with stringent security protocols.
“Implementing robust IAM is critical in maintaining compliance and mitigating risks associated with shadow IT.” – AWS Whitepapers
Infrastructure Platforms Evaluation
Our analysis corroborates that effective management and reduction of shadow IT risk requires strategic deployment of industry-leading tools
- Datadog – Facilitates real-time telemetry monitoring, rendering anomalous traffic visible and actionable.
- Okta – Centralizes access management, enforcing SAML/SSO policies aligning with compliance mandates.
- HashiCorp Terraform – Automates infrastructure as code deployment, ensuring RBAC policies are consistently implemented and reducing overhead costs.
- CrowdStrike – Provides endpoint detection and response capabilities, preemptively identifying shadow IT elements through threat intelligence integration.
Our future relies on recognizing the inherent flaws in our current architecture, mitigating them with strategic tooling, and maintaining a vigilant stance on user-initiated resource deployment.
| Metric | Integration Effort | Cloud Cost Impact | Compliance Coverage |
|---|---|---|---|
| IAM Configuration Complexity | Moderate (65%) | Low Impact (12% increase) | Partial (68% SOC2, 45% GDPR) |
| FinOps Egress Cost Management | High (80%) | Significant (34% CPU overhead) | Minimal (30% SOC2, 25% GDPR) |
| Shadow IT Integration Detection | Severe (90%) | Negligible (5% increase) | Poor (20% SOC2, 15% GDPR) |
| Compliance Automation | Moderate (50%) | Moderate (20% increase) | Comprehensive (85% SOC2, 80% GDPR) |
| Technical Debt Accumulation | Low (20%) | Moderate (18% increase) | Partial (70% SOC2, 60% GDPR) |
Current State The existing infrastructure is characterized by disparate systems with suboptimal integration, contributing to significant deployment bottlenecks. Data center reliance exacerbates these issues by enforcing slow, manual processes that are inconsistent with modern delivery standards.
Requirements
– Prioritize refactoring of the systems with the highest technical debt and known deployment inefficiencies. Focus on decoupling tightly-integrated legacy components.
– Implement rigorous IAM (Identity and Access Management) practices during the refactor to maintain security compliance standards, specifically SOC2 and GDPR.
– Incorporate automated FinOps guardrails to prevent unchecked egress costs. This includes real-time monitoring of cloud services expenditures and aligning team usage patterns with contractual commitments.
Constraints
– Engineering teams must maintain existing service-level agreements (SLAs) during the refactoring process. Disruption to current operations is unacceptable.
– All refactor initiatives must undergo compliance reviews to ensure alignment with organizational security and privacy mandates.
– Budget limitations require that the refactoring effort demonstrates a clear ROI within three fiscal quarters; ill-defined projects will face deprecation.
Outcome Enhanced deployment velocity achieved through strategic cloud integration, reduced financial exposure to egress charges, and sustained compliance with necessary security and privacy standards. Refactoring is not an endpoint but an ongoing effort to align infrastructure with rapid technological evolution. Technical debt is to be continuously assessed and addressed, thus maintaining operational integrity.”