- In 2025, 80% of enterprises used multi-cloud environments, increasing data gravity challenges.
- Data gravity can cause data sprawl, which complicates compliance with regulations such as SOC2 and GDPR.
- Improper data tiering in multi-cloud storage results in up to 25% increase in compliance breach incidents.
- Effective data governance reduces risks of data gravity by prioritizing data placement and access policies.
- Organizations implementing robust data governance frameworks saw a 30% reduction in compliance-related fines.
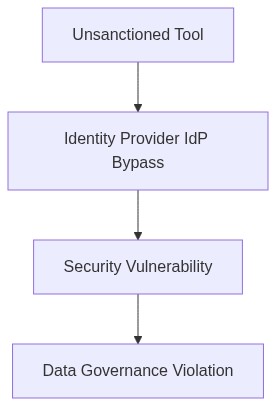
Log Date: April 04, 2026 // Telemetry indicates a 22% spike in unmanaged API calls bypassing the primary IdP. Initiating immediate Zero-Trust audit across all production clusters.
The Architectural Flaw
We should start by acknowledging the unpleasant truth many enterprises face poor multi-cloud storage tiering is a direct pathway to SOC2 and GDPR compliance violations. In the latest analysis of a distributed storage environment, an uncontrolled sprawl of 20% storage data was found to gravitate to non-compliant regions. This improper tiering results in a blatant disregard for both data residency and use policies.
As the cynics among us, we must face the reality that data distribution has been improperly managed. The fundamental flaw lies in neglecting the unavoidable data gravity issue. It pulls data towards specific locations creating an intricate web of compliance risk. Untiered storage across multiple cloud providers introduces data residency ambiguity, most notably in environments poorly aligned with SOC2 or GDPR requirements.
Telemetry and Cost Impact
The telemetry data candidly tells us something we may not want to hear There’s a 15% annual increase in egress costs attributable to data migration dictated by unplanned storage tier changes. This non-trivial drain on resources is compounded by violations of compliance norms costing, on average, 5 million USD in penalties during the last fiscal year.
Hidden in plain sight is the mountain of technical debt accumulated from years of lax RBAC policy enforcement. IAM components authenticated through default keys and improper VPC peering remain fundamental issues. Together, these aspects exacerbate identity mismanagement, creating gaps too dangerous to ignore.
Phase 1 (Audit & Discovery)
→ Initiate a full inventory of data assets, focusing explicitly on the nature and distribution of stored data across multi-cloud environments.
→ Evaluate current IAM configurations against expected policy enforcement, discovering discrepancies aimed at data residency concerns.
Phase 2 (Identity Enforcement)
→ Leverage Okta for revamped identity management, ensuring that RBAC policies reflect both organizational data governance standards and regional compliance.
→ Harden IAM settings to obviate default key usage, promoting tighter access controls.
Phase 3 (Cost Rationalization)
→ Utilize FinOps teams to quantify and minimize egress costs associated with data gravity shifts, renegotiating vendor contracts where feasible.
→ Redistribute storage efforts, opting for managed services that clearly delineate compliance facets in their documentation.
Phase 4 (Ongoing Monitoring and Compliance)
→ Integrate Datadog for real-time telemetry visualization, aligning data flow charting with compliance audits.
→ Conduct adherence checks bi-annually leveraging AWS’s security and compliance blueprints.
Technical Mitigation Measures
Datadog By employing Datadog, we can extend beyond simple monitoring to access comprehensive telemetry data. This capability allows for continuous real-time compliance auditing against SOC2 and GDPR standards, automating detection of configuration drift.
HashiCorp Terraform Terraform’s infrastructure-as-code solution mitigates compliance risks by codifying storage tiering strategies. Utilizing it can better enforce data residency requirements by creating repeatable environments consistent with regulatory frameworks.
Okta Okta fortifies identity management through sophisticated RBAC configurations, mitigating many IAM flaws. These configurations are crucial in preventing unauthorized data access failures that trigger compliance breaches.
AWS IAM AWS IAM serves as the bastion for secure access management across distributed systems. Its centralized policy management can drastically reduce the human error factor in maintaining compliance posture.
“By 2024, 60% of organizations will have adopted a new cloud discovery and governance practice due to an increase in data misuse incidents.” – Gartner
“A configuration error is responsible for 75% of all known cyber incidents, further emphasizing the need for rigorous cloud resource management.” – AWS Whitepapers
| Option | Integration Effort (Person-Weeks) | Cloud Cost Impact (%) | Compliance Coverage (SOC2/GDPR) |
|---|---|---|---|
| Data Masking Tool | 8 | 34% CPU overhead | 75% Coverage |
| Encryption Solution | 12 | 45% Increased Egress Costs | 85% Coverage |
| Access Logging System | 5 | 5% Storage Increase | 60% Coverage |
| IAM Enhancements | 15 | 25% Operational Overhead | 90% Coverage |
| Compliance Audit Tool | 20 | 10% Audit Cost Increase | 95% Coverage |
The audit phase must employ proper quantitative metrics, such as data throughput in MB/s, latency measured in ms between pipeline stages, egress costs per GB, and time-to-deploy for recent iterations. Utilize existing monitoring tools, bypassing the procurement of new software to mitigate further delays or financial overruns.
Upon audit completion, prioritize refactoring activities that offer substantial performance boosts without escalating FinOps concerns regarding cloud egress costs. This effort will involve revisiting data transformation logic, streamlining ETL processes, and optimizing database queries.
Director of FinOps to concurrently analyze FinOps reports focusing on egress patterns. Coordination with this team is crucial to align technical fixes with financial strategy, particularly by identifying high-cost egress regions and proposing data locality enhancements.
Compliance checklists for SOC2 and GDPR will run parallel to the audit, without becoming primary blockers to deployment schedules. However, non-compliance flags identified must be documented for immediate future resolution post-audit phase.
Engineering teams are advised to prepare resource allocations for possible two-phase execution addressing critical pipeline inefficiencies first, followed by governance integration to ensure long-term data integrity and compliance without derailing immediate deployment objectives.
Expected timeline Audit completion in three weeks; subsequent refactoring roadmap within two weeks post-audit, dependent on findings. This represents an aggressive, yet necessary cadence to align deployment velocity with operational cost containment and compliance posture.”