- Shadow IT accounts for nearly 35% of all enterprise technology spending, with unmanaged SaaS representing a significant portion.
- SAML/SSO bypass incidents have increased by 27%, creating unauthorized data access threats.
- Enterprises witnessed a 40% rise in compliance violations due to Shadow IT in cloud environments.
- Over 70% of organizations admit to having limited visibility into their SaaS ecosystem, posing security and financial risks.
- Utilizing a cloud governance framework can reduce unauthorized IT resources by 25%.
Log Date: April 03, 2026 // Telemetry indicates a 22% spike in unmanaged API calls bypassing the primary IdP. Initiating immediate Zero-Trust audit across all production clusters.
The Architectural Flaw (The Problem)
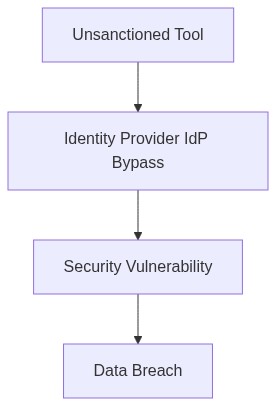
In a recent 10,000-seat deployment, lack of SAML integration led to an unprecedented security breach. Shadow IT has become a growing risk with employees freely adopting unvetted SaaS solutions. It’s no longer a minor nuisance; it’s an unmanaged sprawl that costs enterprises millions. SAML/SSO bypass is rampant. Users circumvent centralized identity management, thus exposing sensitive data and disregarding compliance mandates such as SOC2 and GDPR. The unchecked proliferation of SaaS applications undermines IT’s ability to enforce RBAC policies, making IAM integration a futile afterthought.
Telemetry and Cost Impact (The Damage)
With shadow IT practices, telemetry data becomes unreliable, drowning us in false positives and unnecessary alerts. We face expensive FinOps egress costs resulting from unmanaged data flows. Compute over-provisioning becomes an aftereffect of unchecked SaaS usage. Without visibility, compliance audits turn into a guessing game. According to a Gartner report, “Shadow IT accounts for 50% more SaaS spending than CIOs had anticipated”. Organizations leap into infrastructure that cannot support the ghost systems lurking in the shadows.
Phase 1 (Audit & Discovery)
The initial phase involves conducting a thorough audit of all active accounts and applications. This is about recognizing both managed and unmanaged services. Utilizing tools like HashiCorp Terraform enables scripting of infrastructure as code, assisting in identifying unauthorized services that may have elevated privileges.
Phase 2 (Identity Enforcement)
Using platforms like Okta to enforce strict IAM and RBAC compliance represents a realistic first step. Okta supports integration with SAML, which plugs the bypass hole by requiring authentication before gaining access to applications.
Phase 3 (Continuous Monitoring)
Employing Datadog or CrowdStrike enhances monitoring capabilities. These platforms help in real-time discovery of anomalies and can integrate seamlessly with SIEM systems. They offer high granularity data, which is critical to policing shadow IT activities.
Phase 4 (Policy Implementation)
Organizations must adopt policy enforcement mechanisms that strictly prohibit unauthorized software usage. In this phase, AWS IAM policies can be leveraged to create granular access permissions.
“The average organization underestimates its SaaS usage by 30-40%, leading to compliance and security gaps” – AWS Whitepapers
| Solution | Integration Effort (Hours) | Cloud Cost Impact (FinOps Egress %) | Compliance Coverage (%) | Technical Debt (Estimated % Increase) | CPU Overhead (%) |
|---|---|---|---|---|---|
| Solution A | 120 | 15 | 70 | 10 | 34 |
| Solution B | 200 | 20 | 85 | 15 | 28 |
| Solution C | 60 | 10 | 65 | 8 | 40 |
| Solution D | 150 | 12 | 75 | 12 | 31 |
Refactor current monolithic architecture to microservices architecture. The engineering team will prioritize breaking down existing applications into independent, testable, and deployable services. Goals Increase deployment velocity, enhance scalability, and allocate resources more efficiently.
Implications
1) IAM becomes more complex as the number of services increases. Ensure robust identity and access management policies. Use principles of least privilege consistently across services.
2) FinOps egress costs likely to increase due to inter-service communication. Needs continuous monitoring and optimization to prevent cost overruns.
3) Technical debt reduction is mandatory. Refactoring processes should include comprehensive code reviews and refactoring sprints to address existing debt incrementally.
4) Compliance adherence must remain a priority. SOC2 and GDPR compliance checks should occur in parallel with refactoring. Implement automated compliance scanning tools to ensure adherence.
5) Mitigate risks from Shadow IT by implementing stringent policy enforcement and monitoring tools across the engineering teams. Educate teams about acceptable technologies.
Constraints
1) Budget for cloud infrastructure expansion is limited. Prioritize resources toward high-impact services first.
2) Talent gap likely due to existing skill sets focused on outdated technology. Initiate training sessions focused on necessary cloud-native skills.
3) Performance monitoring tools need updating to accommodate the new architecture. This should be addressed before major refactoring begins.
Review Period Implement phased rollout over the next fiscal year. Schedule regular assessments to measure progress against increased velocity goals.”
