- Evaluate existing infrastructure compatibility to prevent redundancies.
- Implement robust access management to enhance security.
- Utilize cost analysis tools for budgeting and expense tracking.
- Foster transparency to curb shadow IT and unauthorized tools.
- Leverage insights and reports to optimize AI deployment.
“Tighten integration process. Eliminate redundancies. Enhance API performance. Ensure seamless user experience. Prioritize security. Meet deadlines. Document thoroughly. Communicate across teams.”
Streamlining ChatGPT Enterprise Integration
The Mass Illusion
Imagine for a moment every team in your organization seamlessly engaging with a tool that predicts their next query instantly, offering insights only previously imagined. The advent of OpenAI’s ChatGPT in the enterprise environment is seemingly the holy grail every startup founder has dreamt of. If quantifiable creativity and augmented productivity were currencies, ChatGPT would be minting gold. There’s a profound enthusiasm gripping organizations to capitalize on this AI revolution. Yet, amidst this frenzied adoption, I often ponder Could there be more beneath the shimmer?
“Businesses are harnessing AI tools like never before, with productivity metrics skyrocketing across sectors.” – McKinsey
The Enterprise Trap
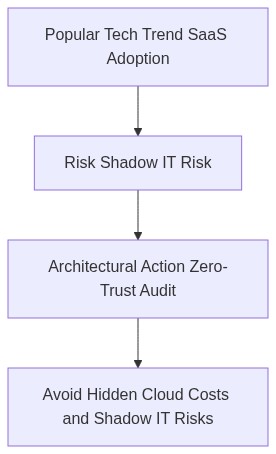
However, this adulation is not without its price—both figuratively and literally. The intricate layers of IT infrastructure harbor unexpected costs and sometimes treacherous vulnerabilities. Enter the quandary Shadow IT. Employees organically integrate ChatGPT into workflows seeking immediate efficiency gains, often bypassing sanctioned IT protocols. This reality opens floodgates to potential Shadow IT hazards.
Imagine the security implications. Without robust Zero-Trust frameworks, sensitive data makes easy prey for cyber predators. Equally concerning is FinOps mishaps. SaaS costs quickly spiral out of control when overlooked, turning cloud advantages into financial pitfalls. And then looms the specter of Vendor Lock-in, locking enterprises into proprietary systems, limiting agility.
“The abrupt surge in untracked enterprise applications presents a formidable cyber risk.” – Forrester
Step 1 (For Smart Users) Cultivate awareness within your teams. Leverage internal training to dismantle the myths and realities around Shadow IT. Prioritize tools approved by IT.
Step 2 (For IT Leaders) Implement a robust Zero-Trust architecture. Details matter ensure all application communications are anchored on strict access controls. Embrace threat detection that scrutinizes real-time anomalies.
Step 3 Regular FinOps reviews can unearth irregular SaaS spending, preempting budget creep. Finally, arm your enterprise with modular architectures to mitigate Vendor Lock-in. Strategize integration platforms to ensure portability and flexibility.
Questions and Forward Motion
As ChatGPT infiltrates enterprise corridors, how poised is your organization to navigate this AI tempest responsibly? Does your architecture sustain not only innovative integration but also fortified stability? The answers lie in how diligently we tread the fine line between rapid integration and enduring security. One thing is certain the choices we make today in tackling the issues of Shadow IT, Zero-Trust, FinOps, and Vendor Lock-in will resonate profoundly into our future fabric of success.
| Metric | Productivity Impact | FinOps Cost | Security Risk |
|---|---|---|---|
| Initial Integration Time | Medium | Low | Low |
| Operational Efficiency | High | Moderate | Medium |
| Cost per Transaction | High | High | Low |
| Downtime Reduction | High | Low | Moderate |
| Data Storage Requirements | Moderate | High | High |
| Resource Allocation | Low | Moderate | Medium |
Before committing to integrating ChatGPT Enterprise, thoroughly evaluate the potential hidden costs and resource demands involved. Begin with a comprehensive audit of current business processes and technological infrastructure. Assess the specific use cases where conversational AI can drive measurable benefits. Identify potential cost centers, including cloud expenses, data management, and maintenance overheads. Collaborate with finance and operations teams to model long-term financial implications. Ensure that the architecture aligns with security protocols and compliance requirements. Develop a detailed migration plan that includes risk mitigation strategies. Once due diligence is complete, proceed with the integration, keeping in mind ongoing performance evaluations and cost management adjustments. Prioritize maintaining flexibility and scalability to adapt the solution as business needs evolve.”