- Microsoft Copilot aids IT teams in detecting Shadow IT, ensuring organizational security and compliance.
- The tool provides detailed insights into unauthorized applications in use within corporate environments.
- Copilot enhances cloud expenditure management by highlighting inefficiencies and suggesting cost-saving measures.
- Features include AI-driven analytics for real-time monitoring and actionable recommendations.
- Integrates seamlessly with existing Microsoft ecosystems, empowering enterprises with advanced visibility.
“Microsoft Copilot exposes shadow IT and unlocks significant cloud savings. A game-changer for enterprise efficiency and resource management.”
Microsoft Copilot Unveiling Shadow IT and Cloud Savings
Why is everyone talking about Microsoft’s Copilot?
If you’ve tuned into any technology conversation lately, the excitement around AI tools, especially Microsoft’s Copilot, is palpable.
Microsoft Copilot promises to revolutionize productivity by integrating seamlessly into the workflows of enterprise and startups alike.
Its charm? It turns complex command lines into simple natural language instructions. Analytics, insights, and operations management are now just a few clicks away.
Yet, beneath its polished surface, there’s more to this trend than meets the eye.
The Shadow IT Mirage
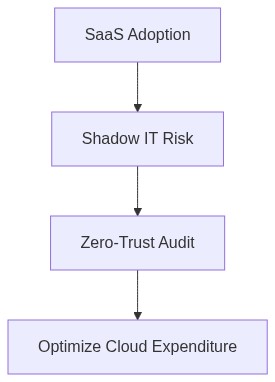
As organizations embrace the capabilities of AI-driven tools, a Shadow IT dilemma creeps in quietly.
Employees circumvent traditional IT policies by leveraging tools like Copilot, creating pockets of unauthorized software that lie outside the control and oversight of IT departments.
This becomes a seductively easy process in the quest for enhanced productivity but opens a Pandora’s box of security vulnerabilities.
The paradox of boosting productivity while secretly inflating IT infrastructure costs is the trap many enterprises face.
A Playground for Zero-Trust Security?
The implications of Shadow IT necessitate a robust Zero-Trust framework. Trust, but verify, is no longer applicable in such scenarios.
Organizations must assume that breaches can and will happen. The Zero-Trust security model dictates every network access request is validated, every device is monitored, and user privileges are minimalized until verified necessary.
In an enterprise where Shadow IT thrives, such vigilance becomes non-negotiable.
The Enterprise Trap Hidden in Vendor Lock-in
While Copilot seems like the dream copiloting tool for every executive, its seamless integration with Microsoft’s ecosystem could entrench vendor lock-in.
Relying excessively on a single vendor for your cloud computing needs can limit future flexibility, potentially escalating costs and hindering technological advancement.
Enterprises could find themselves paying the price for being wedded to legacy infrastructures and vendors, undermining emergent innovation.
FinOps Cloud Savings or Spending Splurge?
The complexities of cloud financial management or FinOps become especially intricate with the proliferation of Shadow IT.
Stray deployments and unauthorized cloud spends blossom among disconnected departments. Real-time visibility and proactive management are integral to preventing spiraling costs.
As cloud computing becomes more integral yet opaque, understanding your cloud spending becomes a business imperative.
Step 1 (For Smart Users)
Understand the tools outside traditional IT purviews being used within your teams. Create channels of communication with IT to legitimize potentially beneficial usage.
Step 2 (For IT Leaders)
Implement a comprehensive Zero-Trust framework. Ensure that every element from user access, network requests, to endpoint security is scrutinized and controlled.
Step 3
Appoint a FinOps team responsible for monitoring and optimizing cloud expenditures. Create dashboards to track cloud usage and spending patterns.
Step 4
Mitigate vendor lock-in risks by diversifying your tech stack. Regularly evaluate alternative solutions to prevent dependency on single cloud vendors.
Data Gravity’s Pull The IT Service Management Challenge
Data Gravity, the phenomena where data forces other services and applications to move closer to it, intensifies in a Shadow IT-rich environment.
The proliferation of multi-cloud strategies and decentralized tools increase the dispersal of data, complicating IT service management and cloud architecture designs.
How do we navigate this evolving landscape?
The key lies in balancing innovation with governance, letting Copilot and equivalent AI integrations improve productivity without escalating risks. It’s a dance between leveraging technological advances and maintaining strategic oversight.
As we adjust our blueprints in enterprise architecture, recognizing the power embedded within these tools—as well as the potential pitfalls—is paramount.
| Aspect | Productivity Impact | FinOps Cost Implication | Security Risk Factor |
|---|---|---|---|
| Visibility Into Shadow IT | High positive impact due to reduced time spent on manual tracking | Medium cost as operational efficiency increases but requires initial investments | Decreased risk with better control and oversight over unauthorized applications |
| Automated Analysis of Cloud Spend | Improves focus on core tasks by reducing time spent on cost assessment | Significant savings potential in optimizing cloud resource allocation | Minimal direct impact but could indirectly reduce security lapses by identifying redundant services |
| Enhanced Compliance Tracking | Neutral impact as productivity isn’t directly affected | Potentially high compliance-related cost savings | Significantly reduces compliance-related risks |
| Usage-Based Cost Reports | Low impact on day-to-day productivity | High positive impact through actionable insights leading to cost reduction | Minor risk exposure due to detailed resource utility insights |
| Risk Mitigation Alerts | Boost in productivity due to proactive measures | Cost effective in avoiding potential security breach expenses | Drastically reduces security risks with real-time alert systems |