- Quantum-resilient architectures leverage post-quantum cryptography to secure data from potential quantum threats.
- Implementing such architectures can reduce the impact of zero-day exploits in supply chain operations.
- Cloud solutions are integrating these technologies to enhance resilience against future threats.
- Organizations must prioritize upgrading existing systems to quantum-safe protocols.
- Increased transparency in supply chain communication is crucial for early zero-day breach detection.
- Collaboration between cloud providers and industry experts is essential for widespread adoption.
“Urgent focus Strengthen cloud infrastructure with quantum-safe protocols. Prevent potential supply breaches, ensuring data integrity and business continuity.”
The Infrastructure Reality
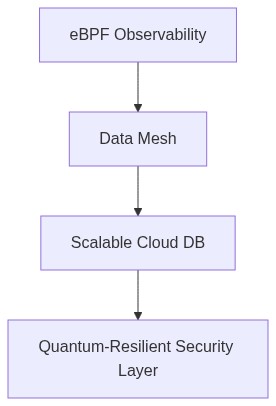
It’s 2026 and the reality of Quantum Computing capabilities threatening cloud security is no longer speculative. With breakthroughs in algorithms capable of undermining classical asymmetric cryptographic systems, CIOs and CTOs need to ensure that their architecture is fortified against such quantum threats. The focus shifts towards quantum-safe cryptographic algorithms and enhancing infrastructure observability using tools like eBPF (extended Berkeley Packet Filter) which permits granular observability without significant overhead. Embracing eBPF in your Linux kernel pipelines facilitates real-time performance analysis and eBPF’s effectiveness in tracing calls can help in identifying potential risks inherent to cryptographic processes.
The use of Mutual TLS (mTLS) may introduce overhead; however, it is imperative for enforcing secure service communication. Implementing mTLS with quantum-resistant algorithms and cipher suites ensures cryptographic resilience. The implementation must be balanced with the understanding that Service Mesh like Istio or Linkerd contributes to increased latency and resource footprint, which impacts overall performance. It’s crucial to measure these trade-offs during early testing phases to appropriately balance against security benefits.
Moreover, Data Gravity concerns are pronounced as data accumulates, increasing its pull, thereby driving the need for distributed data storage strategies. Emphasizing decoupling and decentralizing data exchanges without introducing latency requires utilizing tools such as Apache Kafka to mitigate data gravity challenges effectively.
The Cost (FinOps/TCO) Impact
Investing in quantum-safe infrastructures implicates comprehensive Total Cost of Ownership (TCO) assessments. Leveraging FinOps teams to harness cloud cost management tools is imperative. The deployment of cryptographic measures such as migrating to Post-Quantum Cryptography may introduce significant cost variances from CPU-intensive activities.
Understanding cold-start anomalies is crucial as they can skyrocket costs, especially when transitioning cryptographic functions to serverless environments. These spikes in latency lead to degraded user experience and inefficient resource utilization. Conducting rigorous testing for cold-start behavior under actual workload conditions and simulating peak transaction periods can provide valuable insights into averting these issues.
Confronting vendor lock-in conundrums requires strategic planning, especially as CSPs offer proprietary solutions with differing quantum-safe capabilities. It’s vital to adopt open standards where feasible, and evaluate CSP ecosystems such as those defined by Cloud Security Alliance to ensure portability and flexibility.
Step 1 (Technical config)
Upgrade cryptographic libraries across the infrastructure to support emerging quantum-safe algorithms such as lattice-based, hash-based, and multivariate polynomial cryptosystems. Use Open edX platforms for training development teams on new technologies including PQC enhancements and eBPF for observability improvements.
Step 2 (Risk mitigation)
Conduct bespoke threat modeling sessions focusing on quantum attacks and align security apparatus using quantum-safe handshakes in mTLS. Engage in continuous security awareness drives and adoption workshops to ensure adequate policy compliance across your teams.
Step 3 (Optimization and Performance)
Embrace multi-cluster service mesh topologies to mitigate latency impacts and ensure redundancy. Optimize service discovery mechanisms within your architecture to leverage existing distributed tracing infrastructure for identifying bottlenecks.
Step 4 (Budget Justification)
Establish a FinOps framework for cost forecasting associated with Post-Quantum adoption. Conduct quarterly Business-IT review boards to ensure cost governance aligns with operational objectives and strategic business goals.
Step 5 (Compliance and Governance)
Integrate ongoing compliance regimes with industry benchmarks ready for quantum computing transitions. Develop compliance documentation and contracts that account for quantum resistance parameters reinforced by secure vendor engagements using blockchain for audit trails.
| eBPF Feature | FinOps ROI | Technical Debt | Actionable Insight |
|---|---|---|---|
| Enhanced Network Monitoring | High ROI due to efficient resource allocation | Low Technical Debt if integrated with existing monitoring tools | Prioritize implementation to leverage cost savings and improved security |
| Real-Time Threat Detection | Moderate ROI as it prevents costly breaches | Manageable Technical Debt with phased deployment and training | Focus on incremental roll-out to balance ROI and manage debt |
| Performance Optimization for Quantum Encryption | Potentially High ROI with reduced energy consumption | Significant Technical Debt unless standards are followed | Implement standardization to mitigate debt and unlock ROI |
| Scalable Event Logging | Low to Moderate ROI, dependent on scale | Moderate Technical Debt if not automated | Invest in automation tools to reduce operational costs and debt |
| Proactive Anomaly Detection | High ROI from early threat neutralization | Acceptable Technical Debt with proactive maintenance | Continuous updates and maintenance to ensure sustainability |
