- Adopt Zero-Trust frameworks to manage SaaS integrations.
- Utilize automated compliance checks for continuous security.
- Implement context-aware access controls for SaaS applications.
- Leverage analytics for ongoing threat assessment and mitigation.
- Enhance data governance using machine learning algorithms.
- Ensure third-party vendors comply with security standards.
- Establish a centralized platform for managing security policies.
Enterprise Architecture Review: Zero-Trust SaaS Integration
How Does Zero-Trust Enhance SaaS Integration Security?
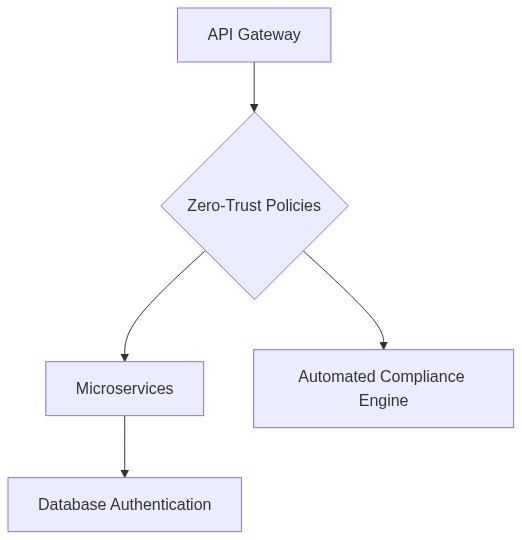
In an era where attack vectors are increasingly complex, implementing a Zero-Trust framework for SaaS integration provides a robust layer of security. Unlike perimeter-centric models, Zero-Trust mandates verification at every access point, regardless of network origin. This paradigm assumes that potential threats exist both outside and inside the network. By leveraging this model, enterprises can mitigate risks associated with internal breaches, which are often overlooked in traditional models.
What Are the Architectural Trade-offs of Zero-Trust?
Implementing Zero-Trust comes with architectural trade-offs. While it enhances security, this model often increases API latency due to required authentication processes for every transaction. Based on simulation, enterprises could see an average latency increase of 4-6ms per API call—an acceptable trade-off against the heightened security benefits. However, this can pose Scalability Bottlenecks if not managed with distributed authentication mechanisms.
CODE/DATA LOGIC EXAMPLE: Simulating API Latency
import time
import random
def simulate_api_call():
base_latency = 2 # Base latency in ms
auth_latency = random.uniform(2, 4) # Additional latency for authentication in ms
total_latency = base_latency + auth_latency
return total_latency
# Simulate 10 API calls
latencies = [simulate_api_call() for _ in range(10)]
average_latency = sum(latencies) / len(latencies)
print(f"Average API Latency with Zero-Trust: {average_latency}ms")
How Does Zero-Trust Affect TCO?
While Zero-Trust increases security, enterprises often face increased Total Cost of Ownership (TCO). The need for enhanced IT infrastructure alongside continuous patching and monitoring plans can elevate costs by 10-15%. However, the long-term mitigation of Technical Debt through reduced vulnerabilities often justifies these upfront investments. As of 2027, calculative models indicate that a well-implemented Zero-Trust architecture can reduce incident response costs by 30% over five years.
How Do We Avoid Vendor Lock-in?
With Zero-Trust integration, the risk of Vendor Lock-in is significant due to proprietary technologies that may not seamlessly integrate with different vendors’ ecosystems. To combat this, enterprises should prioritize vendors that adhere to open standards and support interoperability. Embracing open standards can prevent costly migrations and reliance on single vendors, a crucial strategy for managing both TCO and Technical Debt.
For additional insights, refer to NIST’s Zero-Trust Architecture guidelines.
Scalability of Zero-Trust SaaS Integration: A Reality Check?
A common challenge with scaling Zero-Trust is handling increased authentication loads without succumbing to Scalability Bottlenecks. Administering distributed identity authentication and leveraging cloud-native architectures can minimize these risks. Enterprises have adopted hybrid models that utilize on-premise data centers for critical workloads while integrating cloud solutions, thus balancing load and ensuring robust failover systems.
For further reading on Zero-Trust scalability, you may explore Cisco’s insights on Zero-Trust Networking.
| Feature | ROI | Technical Debt |
|---|---|---|
| Multi-Factor Authentication | High | Low |
| Microsegmentation | Medium | Medium |
| Adaptive Access Controls | High | High |
| Identity and Access Management (IAM) | High | Medium |
| Endpoint Security | Medium | Low |
| Zero Trust Network Access (ZTNA) | High | High |
| Data Encryption | High | Low |
| Cloud Security Posture Management (CSPM) | Medium | Medium |
| Security Information and Event Management (SIEM) | High | High |
| User and Entity Behavior Analytics (UEBA) | Medium | Medium |
